How To Create a Self-Signed Certificate With OpenSSL
Overview
In this lesson, you'll learn how to generate your SSL Certificate and Key for your server.
The purpose of generating SSL (Secure Sockets Layer) keys with OpenSSL is to create a secure connection between your server and clients, protecting sensitive information from being intercepted or compromised by third parties. This is particularly important when transmitting sensitive data such as passwords, credit card numbers, or personal information. Using SSL keys and encrypted connections ensures that your data remains safe and secure as it travels between the server and the client.
Creating a Private Key and Certificate
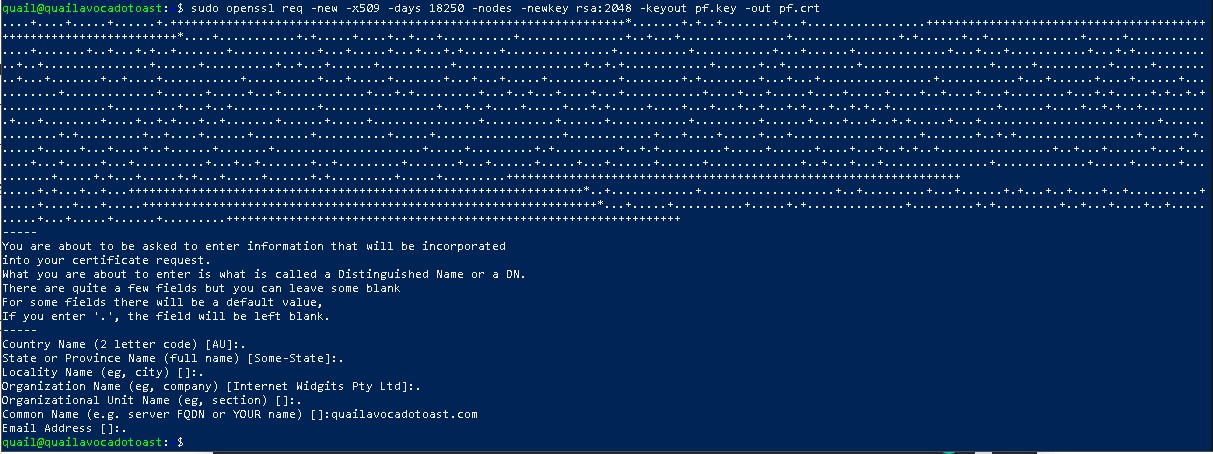
To get started, generate your key and certificate pair with the following command from your Command Line Interface:
sudo openssl req -new -x509 -days 18250 -nodes -newkey rsa:2048 -keyout pf.key -out pf.crtYou can fill this information out if you wish, or if you prefer for your certificate to remain anonymous simply type a period '.' in for each line EXCEPT the 'Common Name' line. On this line you MUST enter your domain name. See the example below.
Now let's make a directory to store our private key (pf.key) and certificate (pf.crt) where we can access them later.
sudo mkdir /etc/tls && sudo mkdir /etc/tls/certs && sudo mkdir /etc/tls/privateNow let's move our new key and certificate into our newly created directory.
sudo mv pf.key /etc/tls/private && sudo mv pf.crt /etc/tls/certsWe're done here. Now we have a secure SSL keypair that we'll use to send encrypted emails from our server. We'll need this after we install Bitwarden on our server.
Congratulations on completing this module! Your server is now hardened and properly secure enough to install the necessary components for Bitwarden.